Help! I’m being attacked from all directions!
March was a bad month for feeling secure in my digital life, and one where I had to really stay on my toes. Within a matter of 10 days, these things happened:
- A book marketer contacted me about promoting my book, and this time I was tempted to take the bait.
- A headhunter contacted me about a job opportunity that looked so convincing I almost responded, until I poked around a bit.
- My Medicare health plan contacted me to let me know that all my personal info was part of a widespread data breach, 6 months ago (this one was real, no spoofing here).
- This followed on the heels of an AT&T data breach that took place in 2024. Shortly after that, someone opened a bank account in my name, at a bank I’ve never done business with, in a city I’ve never lived in (also real).
If that’s not enough to make your head spin, I don’t know what is.
How do we protect ourselves against this onslaught of cybercriminals? It used to be that the worst thing we had to worry about were the spam emails and telemarketing phone calls—people constantly trying to sell us things we don’t want. Now, they are actively trying to steal from us, and that is much worse.
It doesn’t matter that most of us aren’t fabulously wealthy. A few hundred dollars here and there, spread across a wide population, is attractive enough to motivate these thieves.
I must give some credit to SLB, the company I last worked for. Once a year we were required to go through cybersecurity training that covered all aspects of corporate security, including how to evaluate suspicious emails and texts. What follows are the details of how I used some of that training to evaluate the book marketing email and the headhunter email before deciding I should not take their “opportunities” any further.
The book marketer
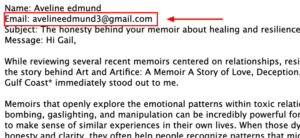
The first red flag was that she was emailing from a Gmail address—anyone with a legitimate business will have their own domain name. It’s the first thing I’ve been trained to check for: the free email address. If they can’t pony up 12 bucks a year for a custom domain name and another hundred bucks to set up a website, chances are, they aren’t legit.
Most book marketers also simply use AI to regurgitate my Amazon book description back to me, and this lady was no exception. Hers was a variation on the same theme:
“Memoirs that openly explore the emotional patterns within toxic relationships such as love bombing, gaslighting, and manipulation can be incredibly powerful for readers who may be trying to make sense of similar experiences in their own lives. When those dynamics are described with honesty and clarity, they often help people recognize patterns that might otherwise remain difficult to name….
I was also moved by the decision to include support resources for readers at the end of the book. That kind of intentional care for people who may be navigating similar circumstances adds an important dimension to the work and reflects the broader impact a memoir like this can have.”
I always like to mess with these people by sending them a few test questions, to see if they’ve even purchased my book. And this lady was quite vague with her language at first, as you can see above. She never really got to the point of why she was contacting me. So my questions were very direct when I emailed her back:
- What exactly are you selling?
- What small town in Texas did the main action in my book take place?
- Can you name one of the support resources I list in the back?
She surprised me by getting #2, Rockport, Texas, correct (which is not in my book description), and she wrote, “… and I understand the beach photo used for the cover was also taken there.” That threw me a bit.
But then I had to stop and think. There are a few ways she could have gotten the fact that the action takes place in Rockport: by doing a reverse image search on my cover photo. It’s a classic picture of Rockport Beach Park on a quiet weekday. Or…Rockport and Houston are mentioned in my author’s bio (also on Amazon), and Houston sure ain’t a “small seaside town in Texas,” so it doesn’t take a mental giant to put two and two together.
But she failed miserably on questions 1 and 3. For #3, she said one of the resources I provided was The National Domestic Violence Hotline, which was a bad guess. I gave local resources for women living in Rockport, Houston, and Spokane.
And for #1, “What exactly are you selling?” this was her answer:
“My work focuses on helping books reach the right readers through a combination of targeted visibility and reader discovery. That includes Amazon optimization, search-based visibility (SEO) (that’s Search Engine Optimization, actually), reader discovery strategies (what?), author website development (already have one, thank you), and Google presence setup for authors who want stronger discoverability online (isn’t this SEO??). I also introduce selected titles to smaller reader communities (we call these book clubs) that enjoy discussing relationship-centered memoirs and personal growth narratives.”
Like all these scammers, this person did not provide a website so I could check out her services or price list, no success stories (where were her successfully marketed books? Her NYT best sellers?), no testimonials from happy customers. My fellow authors and I in the Spokane area alone are being bombarded with these types of emails on a weekly basis. Offers to be put on TV shows and podcasts (for a hefty fee), offers to be represented by literary agents (for a hefty fee), and worse.
I honestly never saw this coming when I decided to self-publish a book, and it’s really the ugly side of the publishing business.
The headhunter
I’ve had my resume up on LinkedIn, Indeed, and other job sites since June 2025, and actively applying for technical editor/writer positions.
This was a different kind of email and a different kind of weird. It did not come from a Gmail address but from a [*.net] address, so I didn’t immediately discount it. A Mr. Ed Rowley said he was doing a candidate search for the company Clovis Oncology, who had an opening for a remote copy editor. He had seen my resume (didn’t say where) and my profile appeared to align with the type of experience they were looking for.
“If you would like to learn more about the opportunity, you are welcome to contact the Hiring Manager, Jose Young, at jyoung@clovisoncologyinc.com. He can provide additional information about the position, responsibilities, and next steps.”
There was no signature line on the email, which was odd; just “Yours sincerely” with nothing afterward. And the Hispanic name of Jose didn’t jive with the last name of Young, but I was willing to give him a pass on that.
The email was quickly followed up by a text message, coming from a different person, alerting me to look for the email and asking me to follow up.
It’s one thing to get an email from a stranger; a text message is something else entirely—that always bugs me. How did they get my private phone number? When I got the text message from a perfect stranger, that put me on edge.
I was tempted to send an email to the guy highlighted in bold above, but something stopped me. Something didn’t feel right.
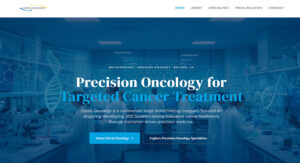
I went online to look for the Clovis company website. They do have one, and on the surface it looks very nice. Very professional. But then I started clicking around. Only about five or six pages are active; the bulk of their site map has been deactivated. They have pages that talk about cancer research breakthroughs and press releases, but it’s all in vague terms. The press releases don’t link to anywhere.
The clincher for me was their About page—I saw no pictures of CEOs or a Board of Directors. For an oncology company? Who works here? Who owns this place?
I finally did a general Google search on the company name and that’s when I hit paydirt. Facebook pages popped up with people complaining about getting scammed by fake job opportunities, bounced checks, and jobs vanishing into thin air.
I read this on LinkedIn, on Clovis’ profile page: “Clovis Oncology is no longer in operation. If you have received any messages regarding potential employment opportunities claiming to be from Clovis Oncology, please be aware that these are not legitimate and may be part of a scam. We strongly encourage you to exercise caution and avoid sharing personal or financial information.”
On Wikipedia, I read that Clovis used to be a legitimate pharmaceutical company, but it filed for bankruptcy in December 2022 after they exaggerated the efficacy of one of their cancer drugs to investors during patient trials.
Well, whew! I dodged a bullet there, and glad I followed my gut instinct. But isn’t it sad that once again, you’ve got people who can’t wait to take advantage of others who are just honestly looking for work?
The Medicare data breach
This one absolutely frosts me. A software vendor contracting with my former health care plan (Wellcare Medicare HMO) had a data breach last fall. So, through no fault of my own, my data has been exposed in a massive hack and Lord knows what they’ll try to do with it.
The letter I received said:
“This data breach occurred between September 17 and 23, 2025. We fixed the problem right away and began a careful review to see what information was affected and who it belonged to. Between December 4 and 18, we gave that information to your health plan (Wellcare) and worked with them to identify who might be affected. You are receiving this letter because your information … date of birth, gender, and health information … was in the compromised files. No Social Security numbers or financial information were in these files.”
So this is my take on the situation. It took potentially 5 days for them to realize something had gone wrong. It took 3 months for them to unravel what the hell happened and whose data was affected. Then they turn the mess over to my health care provider, and it takes them another 3 months to contact us—to let us know that for 6 months, our data has been floating around out there, we have been unaware, and nothing has been done about it. Gee, I just love the fact that this time, my medical information is out there too.
They have offered us 1 year of free credit monitoring through TransUnion, and of course I’ve taken advantage of that. But the dam has already broken, folks—the horse has left the barn. We can be careful and change passwords all we want, but when shit like this happens, what good has all that done? It makes me furious. I’ve already had to abandon one email address because it’s ended up on the dark web, as well as quite a few passwords. I’ve already had a permanent credit freeze placed at all three credit bureaus because of the data breach that occurred at Equifax. What more do we have to do?
The bogus bank account
A few years ago my info was involved in a different data breach. AT&T used to be my home and wireless phone provider, and they had two data breaches in 2024. According to the news reports, these breaches included Social Security numbers, and the data had been released to the dark web. And just like this Medicare breach, they took their sweet old time letting their customers know what happened. I placed credit freezes on my TransUnion, Equifax, and Experian accounts as recommended, but the damage was already done.
About a year later the phone rang. I almost never pick up if it’s a number I don’t recognize, but this day I did. The caller introduced herself as a bank officer from Frost Bank in Corpus Christi, Texas. She gave her full name, position at the bank, and a way I could verify her employment at the bank before we got into the reason for her call.
After these “getting to know you” niceties were over with, she got down to brass tacks: on the previous day, someone had opened a checking account in my name at a Frost Bank branch in Corpus. They used the address where I no longer live in Rockport, Texas as the home address, and used the email address that I’ve now abandoned (because it’s on the dark web) for the account. The information they had that was correct was my Social Security number and cell phone number.
The curious thing about the account setup was that they hadn’t made an initial deposit to finalize the new account. After 24 hours when everything was set except for the initial deposit, the account was flagged as suspicious. That’s when the bank officer decided to contact me to verify whether I had set up the account, or whether this was fraudulent.
They sent an email to the address on record, which bounced. When she tried to call me, luckily I picked up. After the shock of hearing what was going on, I explained to her that: 1) the Rockport address was correct, but I hadn’t lived there since 2018, 2) I had abandoned that email address several years ago, 3) I’ve never done any business with Frost Bank before, and 4) I would have no reason to open an account in Corpus because I don’t even live in south Texas anymore. She was finally convinced that this was a case of attempted identity theft and they would shut down the account.
I asked her, “What on earth would someone do with a checking account in my name? Especially if there’s no money in it?” She said, “I imagine they were thinking they would fund this account with stolen funds from someone else, and then buy goods under your name, or do some other fraud using your name. You know, when people swindle others out of their money, they need a place to deposit that money. They aren’t going to put it in their own personal bank account, are they?”
It really chilled me, as the implications of this sunk in. Because of the outdated nature of the data the identity thief had on me (Rockport was four addresses ago!), there is no doubt in my mind that the info was pulled from the AT&T data breach. I’d been an AT&T customer for about 15 years, most of that time while living in Rockport.
If you’ve ever wondered what people might do with your data once they have it, this is a perfect example.
There is still hope!
All this would be a foreboding post if I didn’t leave you with some hope that we have a bit of control left over our digital lives. There is much we can still do. [Affiliate links below]
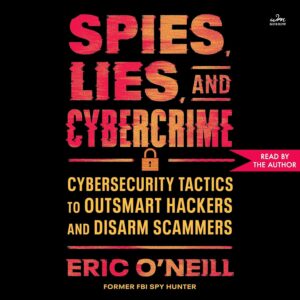 A new book has just been released, written by former FBI agent Eric O’Neill called Spies, Lies, and Cybercrime: Cybersecurity Tactics to Outsmart Hackers and Disarm Scammers, which is brimming with information on ways we can protect ourselves against phishing, malware, and deepfakes.
A new book has just been released, written by former FBI agent Eric O’Neill called Spies, Lies, and Cybercrime: Cybersecurity Tactics to Outsmart Hackers and Disarm Scammers, which is brimming with information on ways we can protect ourselves against phishing, malware, and deepfakes.
O’Neill is someone to be taken seriously—he is the FBI operative who caught the infamous Russian double agent Robert Hanssen, the “most notorious and damaging spy in US history.” (For his undercover work that led to Hanssen’s arrest, read Gray Day.) The case studies that he describes in Spies, Lies, and Cybercrime will make your hair stand on end, and should make any parent think twice before giving their preteen a phone. Here is just a small sample of the cautionary tales in his book:
- A nonprofit charity was brought to its knees by a blackmailer who used the ransomware LockBit (from a Russian cybercrime syndicate) to freeze their global computer network, steal their files, and demand a hefty ransom in bitcoin. As O’Neill was on the staff of this NGO, they had a protocol in place for dealing with cyberthreats, and they eventually outsmarted the criminals.
- A 17-year-old boy got a random message from a beautiful young girl he didn’t know on Instagram. He foolishly got involved in an hours-long chat that led to him sharing a nude photo of himself. The chat then turned sinister: the “girl” started demanding payment, or she would flood his contact list, including his girlfriend, with the photo. He sent $300 but it wasn’t enough, and she demanded more, “or else.” When the pressure got to be too much, he said he might end his life. She told him to do it. The boy, convinced his life was over, got his father’s gun and killed himself. The young girl’s account ended up being an Instagram account purchased and compromised by two brothers in Lagos, Nigeria. They were eventually arrested and extradited to the US, where they are now serving prison time.
- Another 17-year-old named Halima, who came from a strict religious background, came to O’Neill with a related problem. When she was 15, she had sent various nude photos to her boyfriend via the Snapchat application, believing that once she sent the photos, they were deleted from the Snapchat application. But they weren’t deleted. Two years later they were available on the internet by googling her full name plus the words “snap-chat teen pics leaked.” Someone was demanding a $10,000 ransom from her or he would send these photos to her friends, family, and place of worship. The hacker got access to her phone by convincing her to install an app that would scan online merchants to find the best prices on things she routinely purchased.
- A mother received a terrified phone call from her distraught 15-year-old daughter who was supposed to be in Arizona training for ski races. The daughter, frightened out of her wits, was crying, “Mom! Bad men have me! Help! Help!” and then kidnappers came on the line, demanding a million dollars in ransom. The kidnappers had used deepfake technology to mimic her daughter’s voice, stolen from online videos she had posted.
You would think a book on cybersecurity would be dry-bones reading, but O’Neill has woven these true stories together in a riveting fashion so that it is easy reading for the general public. The bigger picture is clear: we are all at risk if we don’t take cybersecurity seriously.
Each chapter ends with a section called “Think like a spy,” with a list that summarizes how cybercriminals operate and how we can protect ourselves against attacks.
The final chapter is called “The Spy Hunter Tool Kit” and is a treasure trove of information. Everything from securing our phone, our social media accounts, our credit card and bank accounts, using passwords, two-factor authentication, romance fraud scams, guidelines for spotting deepfakes in photos, videos, and audio, and more. These are practical things we can do today to help ensure our data is secure and that we won’t be fooled. (For the audiobook version, he provided a 27-page downloadable PDF that has the same information.)
I hope this has been useful and it has caused you to at least change a password or two. For as careful as I’ve tried to be, my data is out there. We are all vulnerable.
If you have any comments, please leave them below. If you feel this would be useful to others, I’d love it if you would share, restack, or subscribe if you’d like to support my writing.


2 Responses
This is a wonderful article, Gail…. very thorough and well-written (of course). Thanks for posting!
Thanks Linda. I’ve taken the next step and changed my email login and password on about 100 accounts that I hold–all my banks, credit cards, every place I shop online, every place I subscribe to. It was a massive undertaking but I am determined to lose these people.